How to Stop a Hacker from Spoofing Your Email
One of the main methods hackers use to hack people is called email spoofing.
Here is an example of Email spoofing: you receive an email from example@abc.com but in reality, this email is not being sent from example@abc.com but from another email sender that is protending to be example@abc.com. This hidden sender will usually send an email with an attachment that contains a virus that will infect the recipient’s computer if opened, or it will ask them to log into one of their accounts like a bank account, website backend, etc… In either case, the intent is malicious.
Email spoofing is possibly the most frustrating abuse issue to deal with because it cannot be stopped, as spoofing is similar to sending a postal letter signing with someone else’s address, as you can imagine, that would be impossible to trace or identify as legitimate.
The Steps to Stop Email Spoofing
- If you become a victim of email spoofing, the most important step is to change your email passwords immediately as well as your cpanel password. This will in most cases prevent the spoofer from being able to continue the attack. You can change your email passwords in “Cpanel account>>Email account>>Password and authentication”. Make sure you choose a password that contains a combination of numbers, characters, and case-sensitive letters. Never reuse your email password on any other website. These steps will help strengthen the security of your account. To change the cpanel password, log into your cpanel – click on Password & Security.
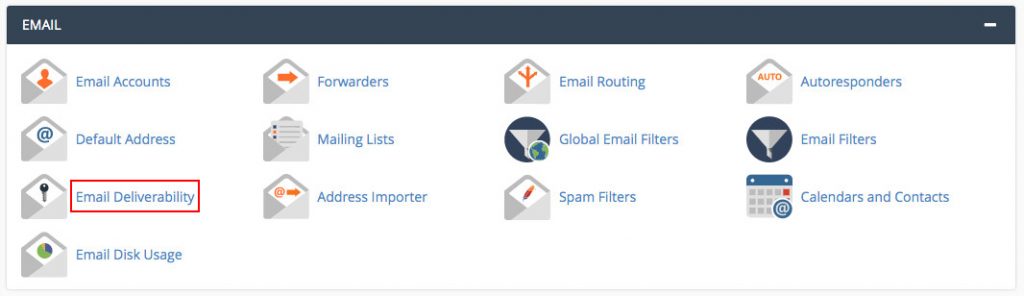
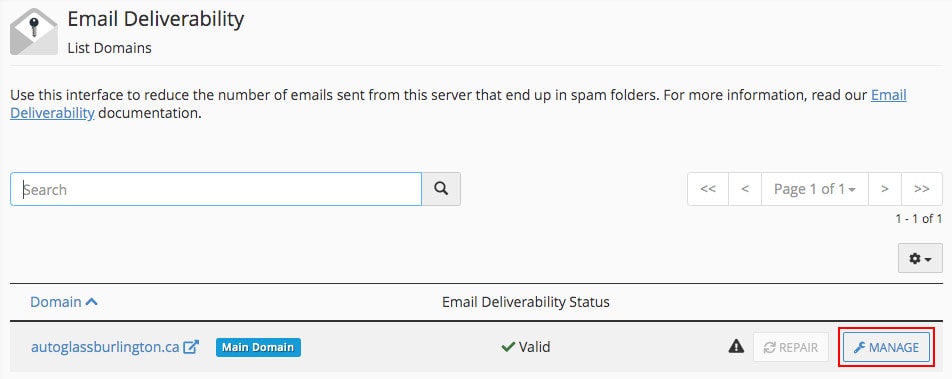
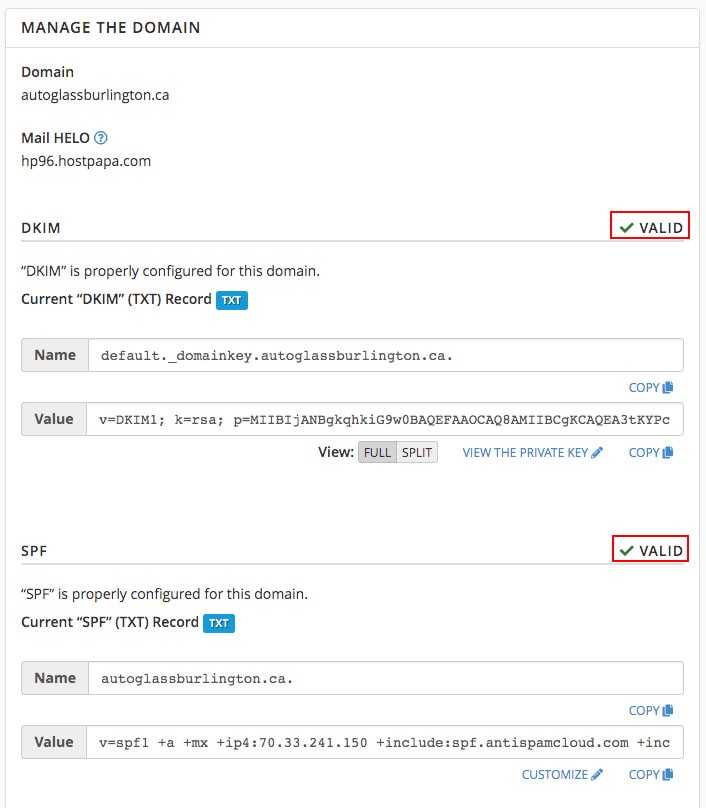
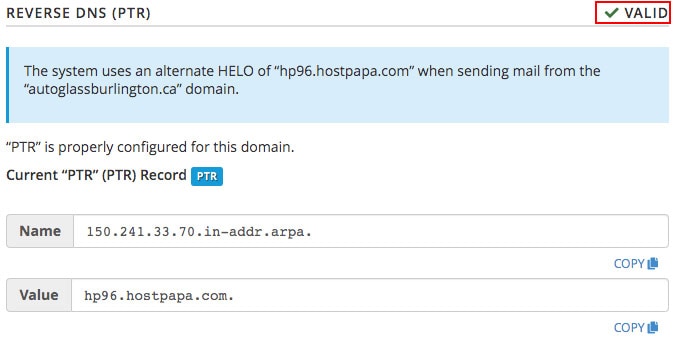
- There are mechanisms such as SPF or DKIM records that might eventually help to reduce the spoofing, however, if the sending server is not configured to validate these (as most likely hacked servers are), the emails will send out using your email address. To enable SPF and DKIM log into your cpanel – click on Email Deliverability – Under your domain click Manage – you will then see if your DKIM and SPF records are enabled or if there are issues with instructions on how to fix them. Alternatively, you can contact your hosting provider and ask them to properly configure DKIM and SPF records for your domain. You can also ask your host if they offer Reverse DNS (PTR) for added security. You can see a visual of the steps to check your SPF and DKIM settings below.
- Make sure your operating system is up-to-date. Be sure you’ve downloaded and installed any critical Windows updates from Microsoft, or Mac OS updates from Apple. It is recommended to keep automatic updates enabled.
- Check for viruses and malware on all devices where you access your email(s). Run a scan on your computer with trusted anti-virus software. If the scan detects any suspicious programs or applications, get rid of them immediately. We suggest using Bitdefender or McAfee Antivirus software.
- Finally, you can use a secure connection when signing in to your email. In cPanel click > Mail Accounts > More > Configure Email Client >
Or if you don’t see More link, then you may see a link that says or Connect Devices. Then use the SSL settings to set up your email client for added security. This setting helps protect your information from being stolen when you are connecting to the mail server.
If this does not solve the spoofing problem, the next line of defence is to change your email service provider. We suggest using Google Suite or Rackspace for email hosting as these two companies have some of the best track records. It is also best practice to separate your email hosting from your website hosting to decrease the chances of being hacked. This also helps to improve stability as servers do go down, and if your web server goes down at least you will still have access to your email and vice versa. However, if your email and web hosting is on the same server, if one goes down, the other will as well.
We hope this helps improve your email and web security and decreases the chances of you facing email spoofing issues in the future.